Introduction
Security isn’t just a “security team” responsibility anymore—it’s a developer’s job too. Most attacks happen due to small mistakes in code or design.
The OWASP Top 10 lists the most critical risks every developer should understand.
Let’s break each one with simple examples + real-world incidents.
1. Broken Access Control
Simple Example:
A user logs in and changes this URL:
/user/profile?id=123 → /user/profile?id=124
Now they can see someone else’s data.
Real Case:
Facebook had issues where users could access other users’ private content due to improper permission checks.
Key Takeaway:
Always enforce access control on the server side.
2. Cryptographic Failures
Simple Example:
Storing passwords like:
password = “123456”
in the database without encryption.
Real Case:
LinkedIn suffered a massive breach where millions of passwords were exposed due to weak hashing.
Key Takeaway:
Use bcrypt/argon2 + HTTPS everywhere.
Simple Example:
Login input:
Username: admin’ OR ‘1’=’1
Password: anything
This bypasses authentication.
Real Case:
Sony Pictures was compromised partly due to injection flaws exposing sensitive internal data.
Key Takeaway:
Use prepared statements. Never trust user input.
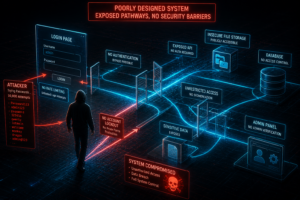
4. Insecure Design
Simple Example:
Login page without rate limiting → attacker tries 10,000 passwords.
Real Case:
Snapchat allowed attackers to scrape millions of users’ phone numbers due to poor API design.
Key Takeaway:
Security should be planned, not patched later.
5. Security Misconfiguration
Simple Example:
Your website is running in debug mode on a live server, showing sensitive errors to users.
Real Case:
A NASA system was exposed due to default authorization misconfiguration, which allowed unauthorized access to internal data.
Key Takeaway:
Turn off debug mode, fix default settings, and keep your system properly configured.
6. Vulnerable and Outdated Components
Simple Example:
You’re using an outdated logging library, and a newly discovered vulnerability allows attackers to execute code on your server just by sending a crafted request.
Real Case:
The Log4Shell exploit in Apache Log4j allowed attackers to achieve remote code execution on thousands of systems worldwide because many applications were running outdated versions.
Key Takeaway:
Always update your libraries immediately when critical vulnerabilities are disclosed.
7. Identification and Authentication Failures
Simple Example:
No limit on login attempts → brute force attack.
Real Case:
Yahoo lost billions of accounts due to weak authentication systems.
Key Takeaway:
Use MFA + secure session handling.
8. Software and Data Integrity Failures
Simple Example:
Installing a package from an unknown GitHub repo without verification.
Real Case:
The SolarWinds Supply Chain Attack compromised trusted software updates and affected thousands of companies.
Key Takeaway:
Verify code integrity and sources.
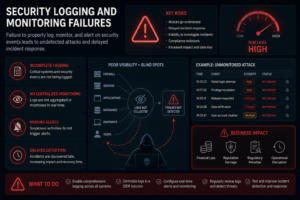
9. Security Logging and Monitoring Failures
Simple Example:
No logs → attacker accesses admin panel and no one notices.
Real Case:
Uber failed to detect a breach affecting millions of users.
Key Takeaway:
Enable logging, monitoring, and alerts.
10. Server-Side Request Forgery (SSRF)
Simple Example:
App fetches a URL entered by user:
http://localhost/admin
Attacker tricks server into accessing internal systems.
Real Case:
Capital One breach used SSRF to access sensitive AWS data of over 100 million users.
Key Takeaway:
Restrict outbound requests and block internal IP access.
Conclusion
These vulnerabilities are not just theory—they’ve caused real-world damage worth billions.
Following the OWASP Top 10 helps you build safer applications and think like a security-aware developer.
The best developers today are not just coders—they are secure coders.