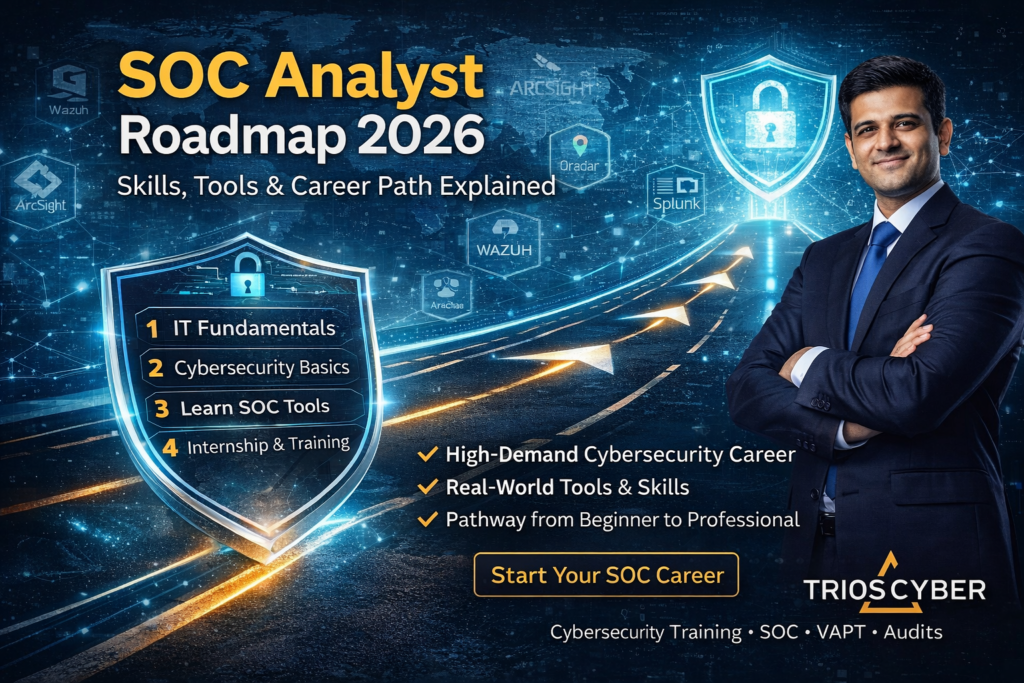
SOC Analyst Roadmap 2026: Skills, Tools, Salary & Career Path Explained
Cybersecurity threats are increasing every day, and organizations across the world are under constant attack. To detect, analyze, and respond to these attacks, companies rely on one critical team – the Security Operations Center (SOC).
A SOC Analyst is the frontline defender of an organization’s digital assets. If you are a student, fresher, or working professional planning a career in cybersecurity, becoming a SOC Analyst is one of the strongest and most stable entry points in 2026.
This blog explains the complete SOC Analyst roadmap, from basics to advanced skills, in a simple and practical way.
What Is a SOC Analyst?
A SOC Analyst (Security Operations Center Analyst) is responsible for:
Monitoring security alerts
Detecting suspicious activities
Investigating cyber incidents
Responding to security threats
Protecting systems, networks, and data
📌 SOC Analysts work 24×7 in shifts to ensure continuous security monitoring for organizations.
Why SOC Analyst Is a High-Demand Career in 2026
SOC roles are growing rapidly due to:
Increase in ransomware attacks
Rise of cloud & remote work
Strict compliance requirements
Shortage of skilled cybersecurity professionals
📌 Organizations prefer SOC Analysts because they provide real-time threat detection, not just preventive security.
Who Can Become a SOC Analyst?
You do not need to be a hacker or coding expert to start.
SOC Analyst roles are suitable for:
Students from any stream
Fresh graduates
Career switchers
IT support professionals
Network engineers
📌What matters most is skills, mindset, and hands-on experience.
SOC Analyst Career Levels Explained
Level 1 – SOC Analyst (L1)
Monitor alerts
Identify false positives
Escalate incidents
Level 2 – SOC Analyst (L2)
Investigate incidents
Perform root cause analysis
Handle malware alerts
Level 3 – SOC Analyst (L3)
Threat hunting
Incident response leadership
Security strategy & automation
Step-by-Step SOC Analyst Roadmap 2026
Step 1: Build Strong IT Fundamentals
Before entering SOC, you must understand:
Networking basics (TCP/IP, DNS, HTTP)
Operating systems (Windows & Linux)
How the internet works
Basic system administration
📌 Without fundamentals, SOC tools will feel confusing.
Step 2: Learn Cybersecurity Basics
You should understand:
Types of cyber attacks
Malware, phishing, ransomware
CIA Triad (Confidentiality, Integrity, Availability)
Authentication & authorization
📌 This builds your security mindset.
Step 3: Understand SOC Concepts
Core SOC knowledge includes:
Security monitoring
Incident lifecycle
Alert triage
Log analysis
Threat intelligence
📌 SOC is more about analysis and decision-making than hacking.
Step 4: Learn SOC Tools (Most Important)
A SOC Analyst must work with real tools such as:
SIEM Tools
Log collection
Correlation rules
Alert generation
Endpoint Security
Antivirus
EDR/XDR platforms
Network Security Tools
Firewalls
IDS/IPS
Threat Intelligence Platforms
IOC analysis
Malware indicators
📌 Hands-on practice is mandatory.
Step 5: Incident Response Skills
SOC Analysts must know:
How to respond to attacks
Containment techniques
Evidence collection
Incident reporting
📌 This is where SOC Analysts prove their value.
Step 6: Documentation & Communication
A good SOC Analyst must:
Write incident reports
Communicate with IT teams
Explain risks to non-technical people
Follow SOPs & playbooks
📌 Cybersecurity is not only technical – communication matters.
Step 7: Internship & Real-World Exposure
Internships are career-changing for SOC roles.
Through internships, you learn:
Live alerts
Real attack scenarios
Shift-based SOC environment
Client handling
📌 Many companies hire interns directly into SOC roles.
SOC Analyst Certifications
Certifications support your profile but do not replace skills.
Recommended:
Entry-level security certifications
SOC-focused training programs
Practical labs-based certifications
SOC Analyst Salary Overview (India & Global)
| Experience Level | India Salary Range (₹ LPA) | Global Salary Range (USD/year) | Demand Level |
|---|---|---|---|
| Entry-Level (0–2 yrs) | ₹3.5 – ₹6 LPA | $40,000 – $70,000 | Stable & Growing |
| Mid-Level (2–5 yrs) | ₹7 – ₹12 LPA | $70,000 – $110,000 | High Demand |
| Senior / Lead (5+ yrs) | ₹15 – ₹25+ LPA | $110,000 – $160,000+ | Excellent Packages |
📌 Salary varies based on skills, SIEM expertise, organization size, and certifications.
Career Growth After SOC Analyst Role
| Next Career Role | Description |
|---|---|
| Threat Hunter | Proactively hunts advanced threats |
| Incident Responder | Manages and contains cyber incidents |
| Blue Team Engineer | Strengthens defensive security controls |
| SOC Manager | Leads SOC operations and teams |
📈 Each role offers higher responsibility, leadership opportunities, and better compensation.
Common Myths About SOC Analyst Roles
❌ SOC work is boring
❌ You must know coding
❌ SOC is only night shifts
❌ SOC has no growth
📌 Reality: SOC is one of the strongest cybersecurity foundations.
How TriosCyber Helps You Become a SOC Analyst
At TriosCyber, we focus on:
Practical tool exposure
Internship-based learning
We train students and professionals with real-world cybersecurity use cases, not just theory.
Final Thoughts
If you want a secure, in-demand, and future-proof cybersecurity career, SOC Analyst is one of the best choices in 2026.
The key is:
✔️ Right roadmap
✔️ Practical skills
✔️ Real exposure
✔️ Continuous learning
Start correctly – and grow confidently.
Want to start your SOC Analyst journey with practical training and internship exposure?
Connect with TriosCyber today.