Introduction
Open Source Intelligence (OSINT) is the process of collecting and analyzing publicly available information to gain useful insights. It is widely used in cybersecurity, ethical hacking, digital forensics, and investigations.
Unlike hacking, OSINT is completely legal when used ethically.
What is OSINT?
OSINT includes data collected from:
- 🌐 Websites
- 📱 Social Media
- 📰 News Articles
- 📂 Public Records
- 🌍 Domain & Network Data
Example: Finding employee emails of a company using public tools.
Importance of OSINT in Cybersecurity
- 🔍 Reconnaissance (Footprinting phase)
- 🛡️ Threat Intelligence
- 👨💻 Social Engineering Prevention
- 🕵️ Digital Investigations
- 🏢 Corporate Security
Types of OSINT Data
- Structured Data – databases
- Unstructured Data – social media, images
- Semi-structured Data – JSON, logs
🛠️ Free OSINT Tools
🔎 Investigation Tools
- Maltego
- SpiderFoot
- theHarvester
- Recon-ng
🌐 Network & Domain Tools
- WHOIS
- Shodan
- Censys
📧 Email & Username Tools
- Hunter.io
- Have I Been Pwned
- Sherlock
🖼️ Image & Metadata Tools
- Google Images
- TinEye
- ExifTool
PRACTICAL: OSINT Investigation
🎯 Objective
Gather information about a target using only free OSINT tools.
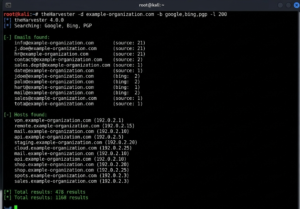
🖥️ Step 1: Domain Recon
Tool: theHarvester
theHarvester -d example.com -b google
👉 Output:
- Emails
- Subdomains
- Hosts
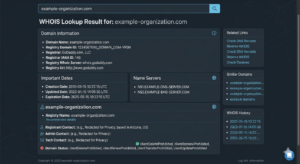
🌐 Step 2: WHOIS Lookup
Tool: WHOIS
👉 Shows:
- Domain owner
- Registration date
- DNS
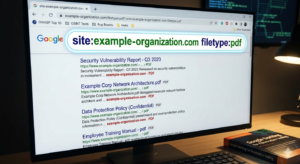
🔍 Step 3: Google Dorking
site:example.com
filetype:pdf site:example.com
intitle:”index of” example
👉 Finds:
- Hidden files
- Public documents
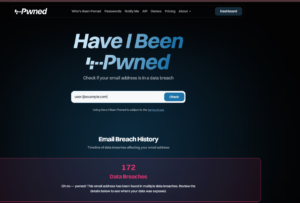
📧 Step 4: Email Breach Check
Tool: Have I Been Pwned
👉 Check leaked emails
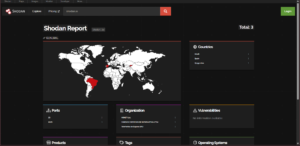
🌍 Step 5: Device Intelligence
Tool: Shodan
👉 Shows:
- Open ports
- Services
- Vulnerabilities
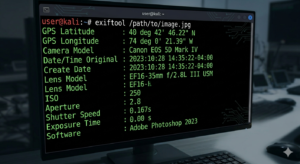
📸 Step 6: Image Metadata
Tool: ExifTool
exiftool image.jpg
👉 Extract:
- GPS location
- Camera info
- Time
⚠️ Legal & Ethical Use
- ✅ Use only public data
- ❌ No unauthorized access
- ⚖️ Follow IT laws
- 🧠 Ethical usage only
Advantages
- Free
- Legal
- Beginner-friendly
- Powerful intelligence
Limitations
- Data may be outdated
- Time-consuming
- Needs verification
Conclusion
OSINT is a must-have skill in cybersecurity, especially for reconnaissance and investigation. With the right tools and ethical practices, it becomes a powerful and legal way to gather intelligence.